Fraud is a term used both in English and Indonesian to define actions requested by the advertiser (views, clicks, installs, site visits, etc) performed by bots or users uninterested in the product. Advertising platforms, aggregators and agencies can use fraud to reach KPI for traffic quality and volume.
From 4% to 90% of the advertising budget can be spent on fraud traffic, according to the data provided by the mobile analytics tool Adjust. Fraud makes advertisers lose money and get distorted data about users’ behavior.
Advertisers often have no idea about the number of contractors in the chain and may be unaware of getting fraud traffic. But avoiding it completely is almost impossible even if there are no middle men. Such traffic can come directly from the websites.
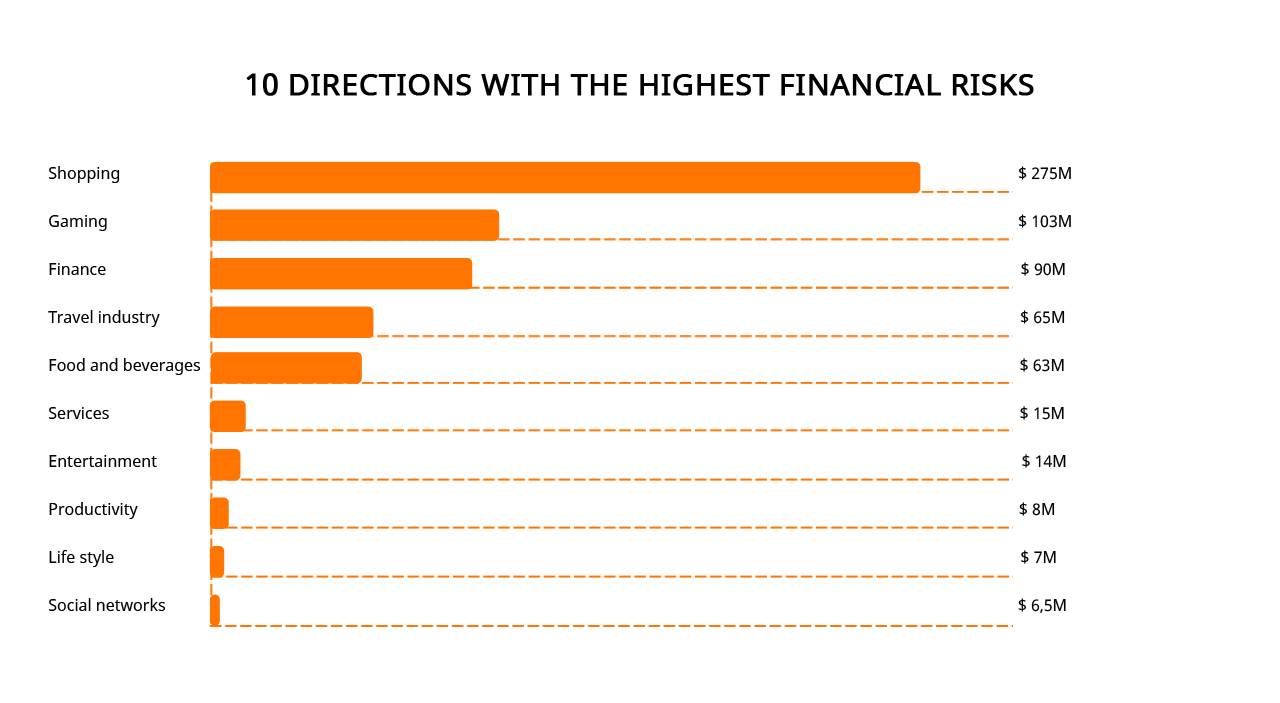
The rating of app categories with the highest level of fraud
Fraud indicators
1) Unrealistically short time slot between clicks and targeted actions
The standard Internet connection speed allows you to download the app in 30 seconds. Meanwhile, installs from a single channel can take from 2 to 10 seconds. This traffic can be considered fraud.
2) Users behavior after clicking on an ad seems to be done according to a single pattern
The time real users take to make a decision whether to download an application and view website pages differs. They will have a different Internet connection speed and various reasons to visit a website/ check an app.
A channel that consistently shows the same user flow or equal intervals between clicks is likely to be fraudulent.
3) Difference in clicks and installs location for the same user
Any device connected to the Internet has an IP address. It contains information about the region where the person is located. If the user connects via the mobile Internet, the IP address comes from the mobile provider. If the user connects via WiFi, IP comes from an the Internet access point.
Clicking an ad in one region and downloading the app in another is virtually impossible.
One can imagine that you clicked on the link in one city, then boarded the plane, flew to another city/country and opened the app. But a large percentage of such “deferred” installs indicate a low traffic quality from the source.
4) An unusually high number of clicks from one IP/ID
This is the first sign that you are receiving traffic from a bot farm. Although, such an indicator might also show the work done by real people. For example, if con artists reset advertising identifiers of devices they use for frauding and perform fresh installs and targeted actions.
5) Click-to-install conversion rate either too low or too high
If click-to-install conversion rate is below 0.3% with a large traffic flow, you are most likely to face ad click frauds.
Conversion above 30% is also a sign of fraud. Such values are realistic for search ad campaigns. In other cases, installs are likely to be fake.
The same is true for unrealistically high or incredibly low CTR and eCPM. If their values for a specific channel differ from the average too much, you can label the source as a fraud one.
6) Suspicious activity at night
Users within one geo are usually more active in the morning, afternoon or evening. Fraud generating tools can work 24 hours a day. Numerous clicks and installs at night which in their numbers are similar to organic indicators at other times of the day cause suspicion. A source with such traffic needs extra checks.
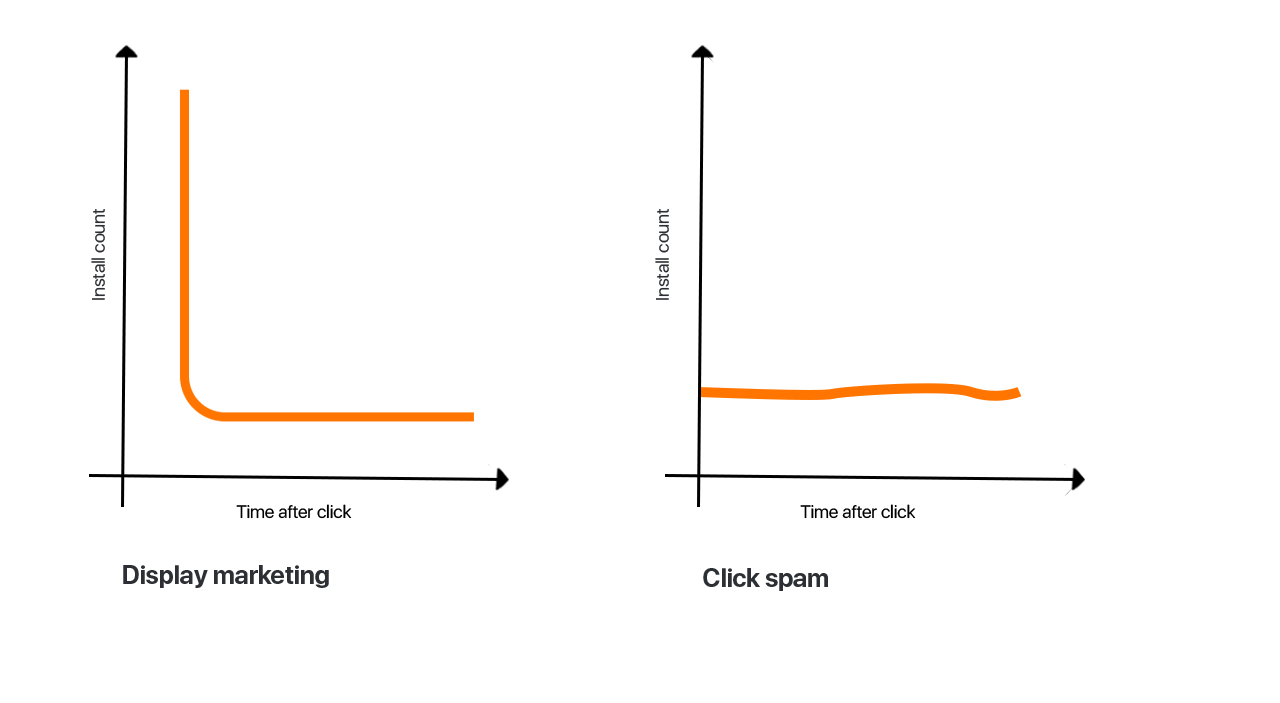
7) A big interval between an ad click and app download
As a rule, most real installs occur during the first hour after the click. By the second hour the number of installs falls sharply. Due to the programs work specificity, in fraud campaigns the installs curve is much more stable.
8) The lack of basic events
If you monitor your “Hello” screen or apps running on and notice these actions do not occur after the install, you are likely to be facing fraud.
Fraudsters can simulate a report on the targeted action performance in the analytics system. Then you will see the install and the necessary in-app activity report, while the steps typical for real users will be skipped.
An extremely low rate retention rate and the removal of the app immediately after its install indicate the incentivized traffic: fraudsters download the app and immediately delete it. A rare, but possible case is when the app has been downloaded by a real user, but for some reason (s)he decided not to use it or just forgot about it.
Types of fraud
SDK spoofing fraud
SDK spoofing is a type of fraud when fraudsters control messages transfer between the SDK application and the server receiving the information.
Initial messages are replaced by those more profitable for the advertiser. For example, banner display statistics – by an app download notification. Thus, you see new installs, which in fact did not occur.
Click-spam
A type of spam when fraudsters add banners in such a way that users are unable to see them and thus click without realizing it. For example, you click on the play button on the site of a free online movie theater and find yourself on a third-party website. Or you play a game inside the app and every click on the screen is counted as a click on the banners that you do not even see. These clicks are counted as ad click conversions.
You are a victim of this type of fraud if:
- the number of organic installs has fallen sharply;
- paying users behave in the same way as those who came after organic installs.
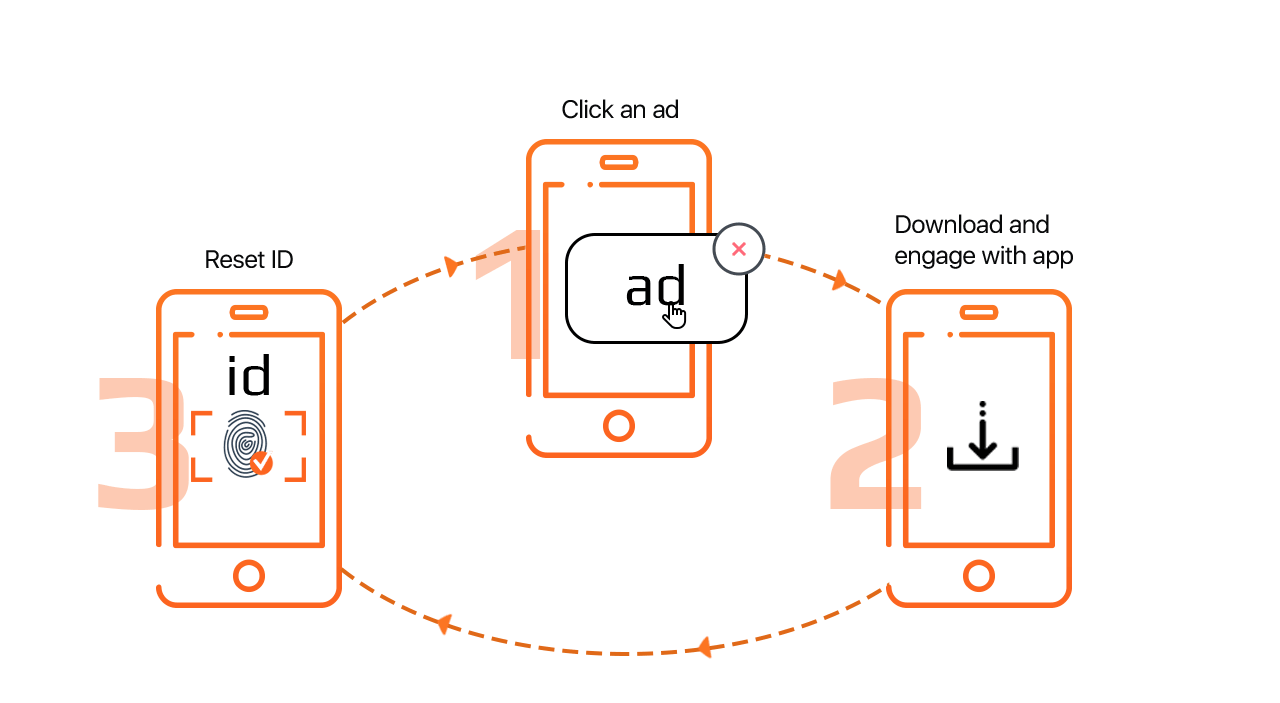
Click injection
In some classifications it stands out as a subtype of click-spam. The user installs an app with a malicious code. Usually, those are fake copies of popular apps or apps from the “tools” category. As a result, the infected device is labelled as a source of fraud.
When the user (even after a long time after the code injection) downloads the desired app, the installation will be counted as coming from a click on the ad, because in the analytics it will have a corresponding label.
Only smartphones with Android operating system can suffer from this type of fraud.
Typically, the attack is indicated by a very short (> 2 seconds) time interval between the click and the install.
Bot traffic
Fraudsters create farms where they put together a large number of smartphones. Devices are connected to the program, which simulates real users’ actions: clicks on ads, app installs, video views, etc.
There is another way of farm organization: instead of multiple devices, a program is used that creates virtual copies of devices with constantly updated IDs. The program simulates real users’ actions in the same way, but this time – on the server.
To prevent themselves from being detected, fraudsters change IP addresses, run traffic through TOR or VPN.
Most likely, your installs are fake:
- if they are immediately followed by app uninstalls;
- if in the analytics there are many clicks/installs from the same IP address.
Incentivized traffic
There are special sites where users are paid for doing certain things: clicks, installs, in-app actions, etc. This traffic is called incentive because users are rewarded for performing targeted actions. Usually the reward is a small sum of money or game currency. On average, it is up to 200 rubles per targeted action.
Sometimes, users are offered to take actions offline. For example, an incentivized user can leave an application for an apartment viewing in a new building and even actually go to check it.
Traffic is most likely to be incentivized if:
- the retention rate from one channel stays low;
- users delete an app immediately after downloading it or download an app without ever trying it later;
- users who download apps for a reward are often send scripts on a particular behavior in the app. For example: download, click on certain buttons and delete in three days. Therefore, in the analytics you can find numerous installs with the same model of behavior.
How to protect yourself from fraud
1) Update your SDK
In new versions, anti-fraud systems are also updated.
2) Discuss risks with contractors in advance
At the beginning of your work with contractors discuss the ways of payment and further cooperation, in case you track fraud.
Include in the contract the description of your steps provided those cases occur. For example, you can specify which traffic indicators in the analytics will be considered fraud and thus will not be paid.
3) Remove contractors with fraud traffic
If you or your anti-fraud system have detected fraudulent traffic, which in large volumes comes from one of your contractors, apply penalties to this company. If this happens repeatedly, then it’s easier to disable the channel that delivers poor-quality traffic.
4) Do not target at suspicious OS versions
Do not target your ads at devices with obsolete or not yet released OS.
Typically, bot farms purchase old smartphones that only support older OS versions. In doing this, you cut off an insignificant percentage of real users, but avoid fraudsters’ attacks.
5) Track analytics
Conversion analysis of IP, device-info, time between click and conversion, user’s life after the app install and conversion through VPN or proxy can help you learn about fraud.
6) Use services with built-in antifraud
Anti-fraud systems are built into some advertising platforms: for example, “Yandex.Direct”, myTarget. But they do not cut off all fraud traffic.
Such mobile trackers and analytics tools a Adjust, Appsflyer, Mixpanel, Tune, etc have their own anti-fraud solutions. They differ in number of functions, services cost and bias. Even clean traffic is sometimes recognized as fraud.
7) Use anti-fraud programs
Anti-fraud programs analyze each conversion, as well as the entire advertising campaign to track fraud sources. Such solutions make it unnecessary for you to check the results of campaigns manually.
Systems can analyze all the campaigns for fraud conversions/sources, or check only the sources you have indicated. You can also set an anti-fraud program to search for a specific type of fraud.
The most famous anti-fraud solutions are Scalarr, Forensiq, FraudScore, Kraken, 24 metrics (FraudShield), Kount, Fraudlogix.
All these programs cost money. To assess the feasibility of investing in an anti-fraud solution, you can test a trial version. If during the trial period the system detects fraud traffic that is equal to the amount of money you paid for it, it makes sense to renew the subscription.